Время на прочтение
4 мин
Количество просмотров 261K
Рэнди Франклин Смит (CISA, SSCP, Security MVP) имеет в своем арсенале очень полезный документ, рассказывающий о том, какие события (event IDs) обязательно должны отслеживаться в рамках обеспечения информационной безопасности Windows. В этом документе изложена крайне полезная информация, которая позволит Вам “выжать” максимум из штатной системы аудита. Мы подготовили перевод этого материала. Заинтересованных приглашаем под кат.
О том, как настроить аудит, мы уже обстоятельно писали в одном из наших постов. Но из всех event id, которые встречаются в журналах событий, необходимо остановить свое внимание на нескольких критических важных. На каких именно – решать каждому. Однако Рэнди Франклин Смит предлагает сосредоточить внимание на 10 важных событиях безопасности в Windows.
Контроллеры доменов
Event ID — (Категория) — Описание
1) 675 или 4771
(Аудит событий входа в систему)
Событие 675/4771 на контроллере домена указывает на неудачную попытку войти через Kerberos на рабочей станции с доменной учетной записью. Обычно причиной этого является несоответствующий пароль, но код ошибки указывает, почему именно аутентификация была неудачной. Таблица кодов ошибок Kerberos приведена ниже.
2) 676, или Failed 672 или 4768
(Аудит событий входа в систему)
Событие 676/4768 логгируется для других типов неудачной аутентификации. Таблица кодов Kerberos приведена ниже.
ВНИМАНИЕ: В Windows 2003 Server событие отказа записывается как 672 вместо 676.
3) 681 или Failed 680 или 4776
(Аудит событий входа в систему)
Событие 681/4776 на контроллере домена указывает на неудачную попытку входа в систему через
NTLM с доменной учетной записью. Код ошибки указывает, почему именно аутентификация была неудачной.
Коды ошибок NTLM приведены ниже.
ВНИМАНИЕ: В Windows 2003 Server событие отказа записывается как 680 вместо 681.
4) 642 или 4738
(Аудит управления учетными записями)
Событие 642/4738 указывает на изменения в указанной учетной записи, такие как сброс пароля или активация деактивированной до этого учетной записи. Описание события уточняется в соответствие с типом изменения.
5) 632 или 4728; 636 или 4732; 660 или 4756
(Аудит управления учетными записями)
Все три события указывают на то, что указанный пользователь был добавлен в определенную группу. Обозначены Глобальная (Global), Локальная (Local) и Общая (Universal) соответственно для каждого ID.
6) 624 или 4720
(Аудит управления учетными записями)
Была создана новая учетная запись пользователя
7) 644 или 4740
(Аудит управления учетными записями)
Учетная запись указанного пользователя была заблокирована после нескольких попыток входа

(Аудит системных событий)
Указанный пользователь очистил журнал безопасности
Вход и выход из системы (Logon/Logoff)
Event Id — Описание
528 или 4624 — Успешный вход в систему
529 или 4625 — Отказ входа в систему – Неизвестное имя пользователя или неверный пароль
530 или 4625 Отказ входа в систему – Вход в систему не был осуществлен в течение обозначенного периода времени
531 или 4625 — Отказ входа в систему – Учетная запись временно деактивирована
532 или 4625 — Отказ входа в систему – Срок использования указанной учетной записи истек
533 или 4625 — Отказ входа в систему – Пользователю не разрешается осуществлять вход в систему на данном компьютере
534 или 4625 или 5461 — Отказ входа в систему – Пользователь не был разрешен запрашиваемый тип входа на данном компьютере
535 или 4625 — Отказ входа в систему – Срок действия пароля указанной учетной записи истек
539 или 4625 — Отказ входа в систему – Учетная запись заблокирована
540 или 4624 — Успешный сетевой вход в систему (Только Windows 2000, XP, 2003)
Типы входов в систему (Logon Types)
Тип входа в систему — Описание
2 — Интерактивный (вход с клавиатуры или экрана системы)
3 — Сетевой (например, подключение к общей папке на этом компьютере из любого места в сети или IIS вход — Никогда не заходил 528 на Windows Server 2000 и выше. См. событие 540)
4 — Пакет (batch) (например, запланированная задача)
5 — Служба (Запуск службы)
7 — Разблокировка (например, необслуживаемая рабочая станция с защищенным паролем скринсейвером)
8 — NetworkCleartext (Вход с полномочиями (credentials), отправленными в виде простого текст. Часто обозначает вход в IIS с “базовой аутентификацией”)
9 — NewCredentials
10 — RemoteInteractive (Терминальные службы, Удаленный рабочий стол или удаленный помощник)
11 — CachedInteractive (вход с кешированными доменными полномочиями, например, вход на рабочую станцию, которая находится не в сети)
Коды отказов Kerberos
Код ошибки — Причина
6 — Имя пользователя не существует
12 — Ограничение рабочей машины; ограничение времени входа в систему
18 — Учетная запись деактивирована, заблокирована или истек срок ее действия
23 — Истек срок действия пароля пользователя
24 — Предварительная аутентификация не удалась; обычно причиной является неверный пароль
32 — Истек срок действия заявки. Это нормальное событие, которое логгируется учетными записями компьютеров
37 — Время на рабочей машины давно не синхронизировалось со временем на контроллере домена
Коды ошибок NTLM
Код ошибки (десятичная система) — Код ошибки (16-ричная система) — Описание
3221225572 — C0000064 — Такого имени пользователя не существует
3221225578 — C000006A — Верное имя пользователя, но неверный пароль
3221226036 — C0000234 — Учетная запись пользователя заблокирована
3221225586 — C0000072 — Учетная запись деактивирована
3221225583 — C000006F — Пользователь пытается войти в систему вне обозначенного периода времени (рабочего времени)
3221225584 — C0000070 — Ограничение рабочей станции
3221225875 — C0000193 — Истек срок действия учетной записи
3221225585 — C0000071 — Истек срок действия пароля
3221226020 — C0000224 — Пользователь должен поменять пароль при следующем входе в систему
Еще раз продублируем ссылку на скачивание документа на сайте Рэнди Франклина Смита www.ultimatewindowssecurity.com/securitylog/quickref/Default.aspx. Нужно будет заполнить небольшую форму, чтобы получить к нему доступ.
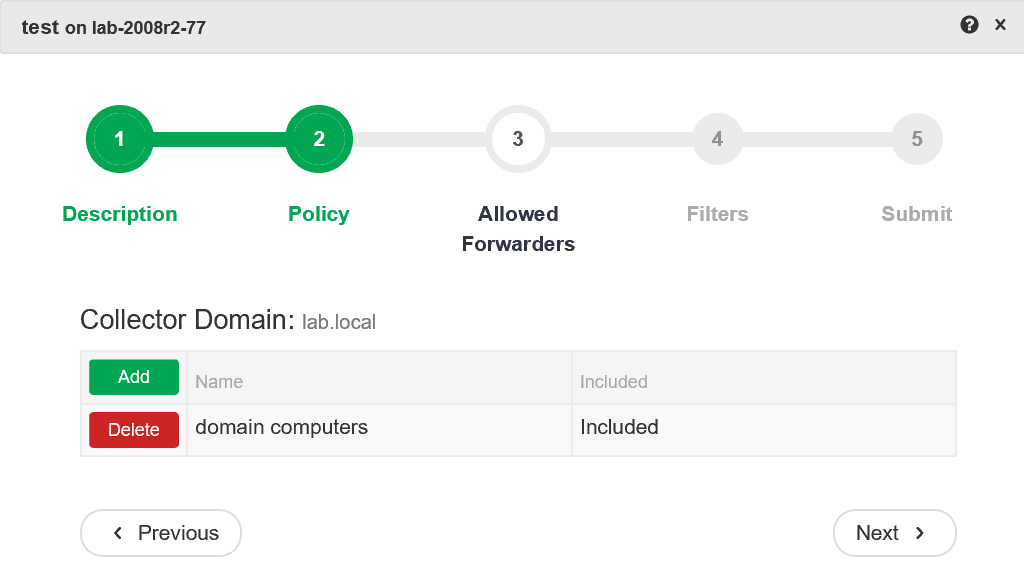
P.S. Хотите полностью автоматизировать работу с журналами событий? Попробуйте новую версию NetWrix Event Log Manager 4.0, которая осуществляет сбор и архивирование журналов событий, строит отчеты и генерирует оповещения в режиме реального времени. Программа собирает данные с многочисленных компьютеров сети, предупреждает Вас о критических событиях и централизованно хранит данные обо всех событиях в сжатом формате для удобства анализа архивных данных журналов. Доступна бесплатная версия программы для 10 контроллеров доменов и 100 компьютеров.
Corrupt system files often trigger this problem
by Henderson Jayden Harper
Passionate about technology, Crypto, software, Windows, and everything computer-related, he spends most of his time developing new skills and learning more about the tech world. He also enjoys… read more
Updated on
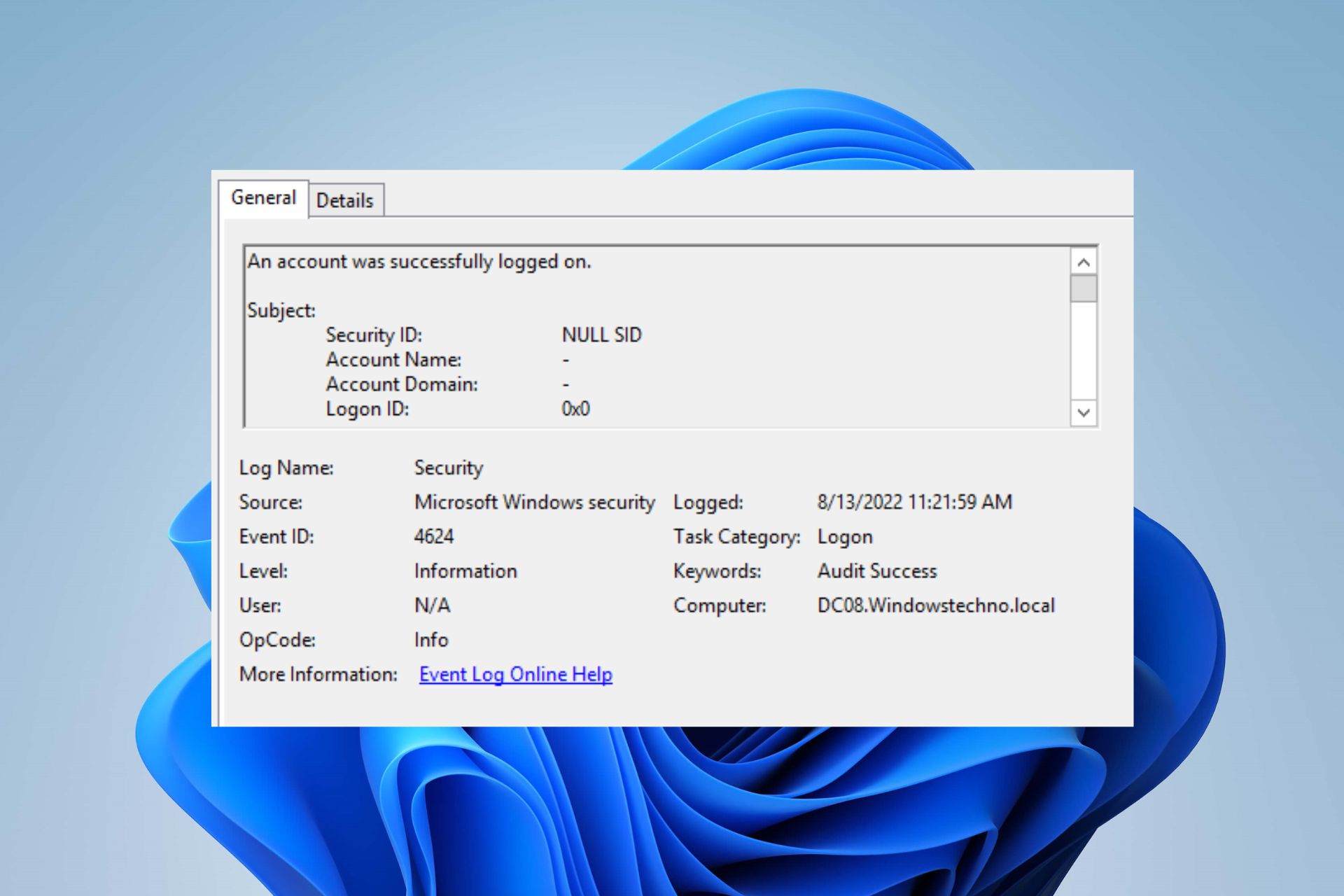
- Event ID 4624 occurs when a logon session is created on the destination computer.
- The event ID can become an issue due to corrupt system files or problems with the Event viewer.
- You may fix the event ID 4624 by performing a Clean boot and running an SFC scan.
Many activities run on the system simultaneously or consecutively to help it perform at its best. These activities are stored in numerous Event IDs, identifying which services they are providing info. However, users report the Event ID 4624 occurring on Windows PC, appearing repeatedly and interrupting user activity.
Also, our readers can read about the Event ID 7023 error on Windows 11 and some fixes to resolve it.
What causes the event ID 4624?
The Event ID 4624 Logon ID 0x3E7 occurs when a logon session is created on the destination machine. It is generated on the computer that was accessed. Also, it indicates the type of logon and other fields like Anonymous logon and Impersonation level.
Some factors that can cause the event ID 4624 on the Domain controller are:
- Corrupt system files – You can encounter event ID 4624 irrelevantly when your system files are corrupted or missing. It causes miscommunication between the system and the services depending on the faulty files.
- Issues with Event Viewer service – Users may experience the event ID appearing on the PC due to the Event Viewer malfunctioning. It causes the event logging process to work incorrectly, displaying the wrong event details on your computer.
- Faulty Windows updates – Installing a recent update can cause issues with the event ID 4624. If the update is corrupt, it blocks the activity of the services running on your PC. So, the event ID can be logged if you have a faulty or corrupt update installed.
Other factors not highlighted above can cause the event ID. Nonetheless, we’ll take you through some steps to fix it.
How do I fix event ID 4624?
Before trying any advanced troubleshooting steps, go through the following:
- Turn off background apps running on your PC.
- Temporarily disable antivirus software on your computer.
- Restart Windows in Safe Mode and check if the event ID persists.
Some PC issues are hard to tackle, especially when it comes to missing or corrupted system files and repositories of your Windows.
Be sure to use a dedicated tool, such as Fortect, which will scan and replace your broken files with their fresh versions from its repository.
If you can’t fix the event ID 4624, proceed with the troubleshooting steps below:
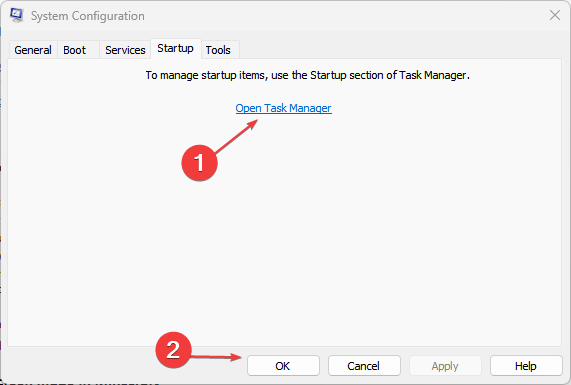
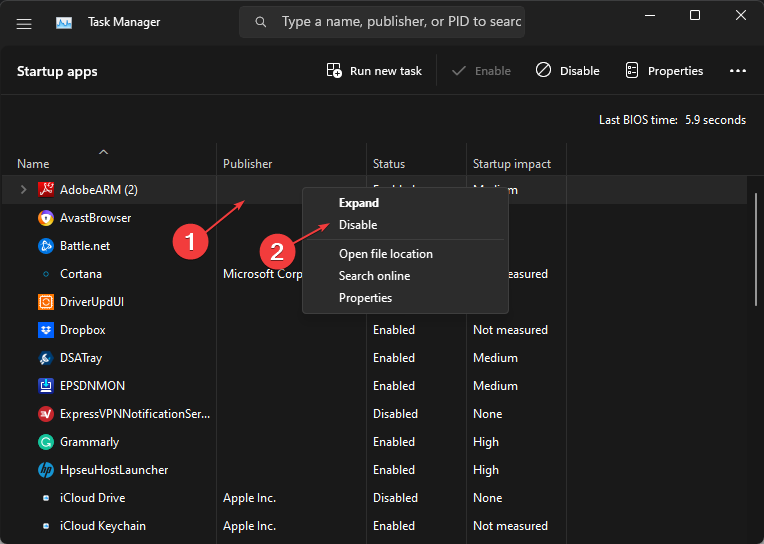
1. Perform a Clean boot on your PC
- Press Windows + R key to open the Run dialog box, type msconfig, and click OK.
- Click the Services tab and check the box for the Hide all Microsoft services option, then click the Disable all button.
- Go to the Startup tab and click OpenTask Manager.
- Select the startup programs and click the Disable button.
- Restart your PC and check if the event ID 7034 error persists.
A Clean boot stops services interfering with other essential features on your PC from running when you start the system. It can resolve the event ID 4624.
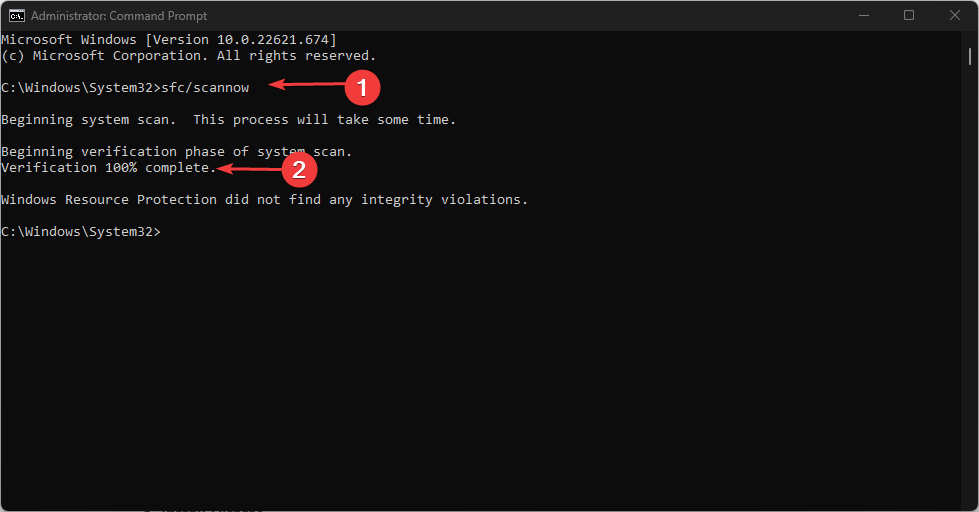
2. Run a System File Checker (SFC) scan
- Left-click the Start button, type Command Prompt, and click the Run as administrator option.
- Click Yes on the User Account Control prompt.
- Type the following and press Enter:
sfc /scannow - Restart your PC and check if the event ID 4624 persists.
Running an SFC scan on your system will detect and repair corrupt system files causing the event ID to occur. Check how to fix the run as administrator option if it’s not working on your PC.
- Fix: Secure Boot is Greyed Out on Windows 11
- Fix: Touchpad Clicks but Doesn’t Move on Windows 11
- Fix: No Internet, Secured Error on Windows 11
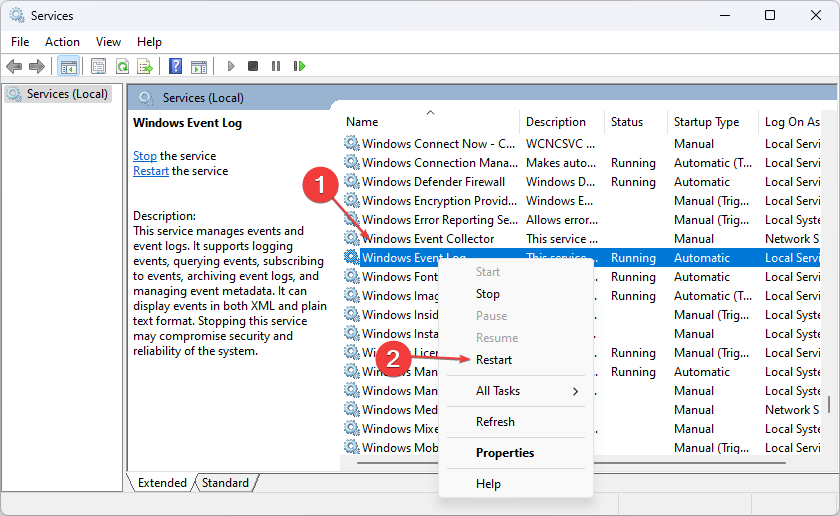
3. Restart Windows Event Log Service
- Press Windows + R key to open the Run dialog box, type services.msc, and press Enter to open the Service manager.
- Find the Windows Event Log service in the services list, right-click on it, and select Restart from the drop-down menu.
- Restart your PC and check if you can fix the event ID 4624 that occurs.
Restarting the Windows Event Log service will help stop and refresh its activities. Also, it will clear off event logs incorrectly logged, causing it to run into errors.
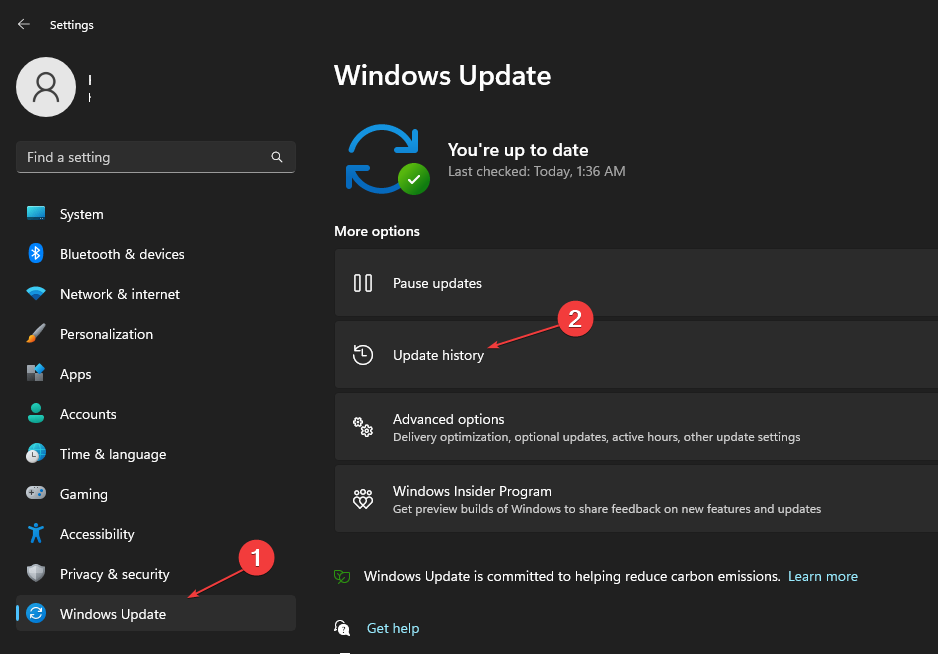
4. Uninstall recent Windows updates
- Press Windows + I key to open the Windows Settings app.
- Go to Windows Update and select Update history from the right pane.
- Click the Uninstall updates button and select the most recent update you installed.
- Click on Uninstall to confirm the removal of the update.
Uninstalling the recent Windows update should help fix any issue with the last build causing the event ID. Check our guide on how to uninstall updates on Windows 11 for more steps.
In addition, our readers can check our article on fixing Application popup event ID 1060 on Windows 11. Also, we have a detailed guide on fixing the Security log is now full – Event ID 1104 on Windows 11.
Should you have further questions or suggestions about this guide, kindly drop them in the comments section below.
При расследовании различных инцидентов администратору необходимо получить информацию кто и когда заходил на определенный компьютер Windows. Историю входов пользователя в доменной сети можно получить из журналов контроллеров домена. Но иногда проще получить информацию непосредсвенно из логов компьютера. В этой статье мы покажем, как получить и проанализировать историю входа пользователей на компьютер/сервер Windows. Такая статистика поможет вам ответить на вопрос “Как в Windows проверить кто и когда использовал этот компьютере”.
Содержание:
- Настройка политики аудита входа пользователей в Windows
- Поиск событий входа пользователей в журнале событий Windows
- Анализ событий входа пользователей в Windows с помощью PowerShell
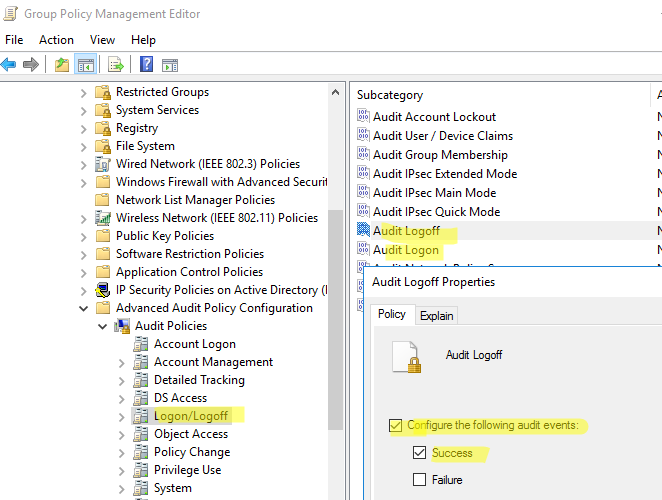
Настройка политики аудита входа пользователей в Windows
Сначала нужно включить политик аудита входа пользователей. На отдельностоящем компьютере для настройки параметров локальной групповой политики используется оснастка gpedit.msc. Если вы хотите включить политику для компьютеров в домене Active Directorty, нужно использовать редактор доменных GPO (
gpmc.msc
).
- Запустите консоль GPMC, создайте новую GPO и назначьте ее на Organizational Units (OU) с компьютерами и / или серверами, для которых вы хотите включить политику аудита событий входа;
- Откройте объект GPO и перейдите в раздел Computer Configuration -> Policies -> Windows Settings -> Security Settings –> Advanced Audit Policy Configuration -> Audit Policies -> Logon/Logoff;
- Включите две политики аудита Audit Logon и Audit Logoff. Это позволит отслеживать как события входа, так и события выхода пользователей. Если вы хотите отслеживать только успешные события входа, включите в настройках политик только опцию Success;
- Закройте редактор GPO и обновите настройки политик на клиентах.
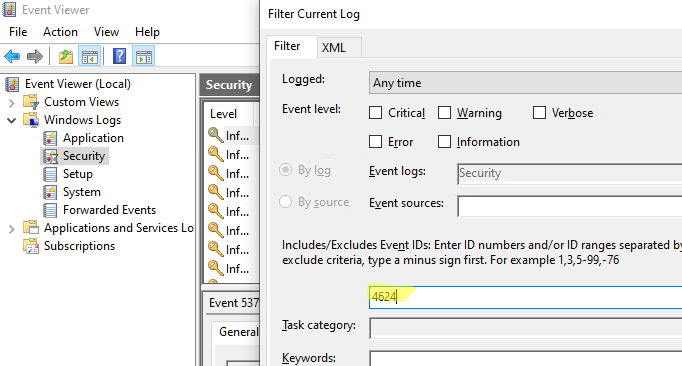
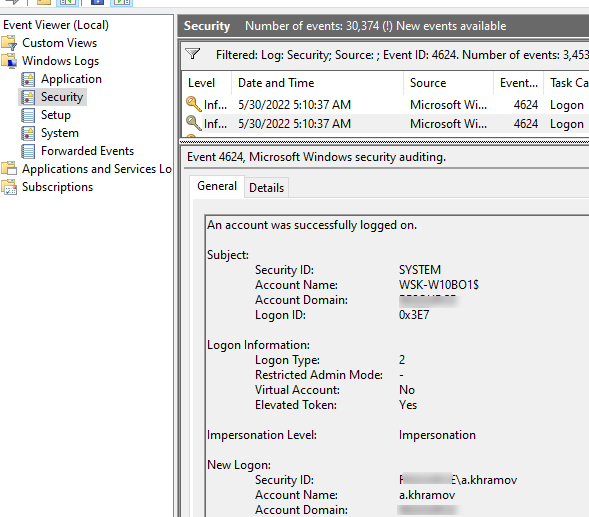
Поиск событий входа пользователей в журнале событий Windows
После того как вы включили политики аудита входа, при каждом входе пользователя в Windows в журнале Event Viewer будет появляться запись о входе. Посмотрим, как она выглядит.
- Откройте оснастку Event Viewer (
eventvwr.msc
); - Разверните секцию Windows Logs и выберите журнал Security;
- Щелкните по нему правой клавишей и выберите пункт Filter Current Log;
- В поле укажите ID события 4624 и нажмите OK;
- В окне события останутся только события входа пользователей, системных служб с описанием
An account was successfully logged on
; - В описании события указано имя и домен пользователя, вошедшего в систему:
New Logon: Security ID: WINITPRO\a.khramov Account Name: a.khramov Account Domain: WINITPRO
Ниже перечислены другие полезные EventID:
| Event ID | Описание |
| 4624 | A successful account logon event |
| 4625 | An account failed to log on |
| 4648 | A logon was attempted using explicit credentials |
| 4634 | An account was logged off |
| 4647 | User initiated logoff |
Если полистать журнал событий, можно заметить, что в нем присутствуют не только события входа пользователей на компьютер. Здесь также будут события сетевого доступа к этому компьютеру (при открытии по сети общих файлов или печати на сетевых принтерах), запуске различных служб и заданий планировщика и т.д. Т.е. очень много лишний событий, которые не относятся ко входу локального пользователя. Чтобы выбрать только события интерактивного входа пользователя на консоль компьютера, нужно дополнительно сделать выборку по значению параметра Logon Type. В таблице ниже перечислены коды Logon Type.
| Код Logon Type | Описание |
|---|---|
| 0 | System |
| 2 | Interactive |
| 3 | Network |
| 4 | Batch |
| 5 | Service |
| 6 | Proxy |
| 7 | Unlock |
| 8 | NetworkCleartext |
| 9 | NewCredentials |
| 10 | RemoteInteractive |
| 11 | CachedInteractive |
| 12 | CachedRemoteInteractive |
| 13 | CachedUnlock |
При удаленном подключении к рабочему столу компьютера по RDP, в журнале событий появится записи с Logon Type 10 или 3. Подробнее об анализе RDP логов в Windows.
В соответствии с этой таблицей событие локального входа пользователя на компьютер должно содержать Logon Type: 2.
Для фильтрации события входа по содержать Logon Type лучше использовать PowerShell.
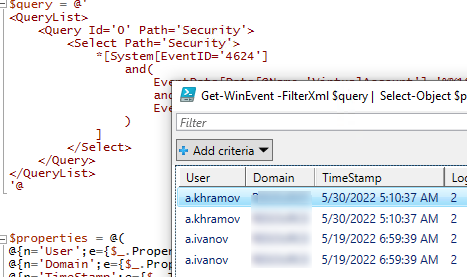
Анализ событий входа пользователей в Windows с помощью PowerShell
Допустим, наша задача получить информацию о том, какие пользователи входили на этот компьютер за последнее время. Нам интересует именно события интерактивного входа (через консоль) с
LogonType =2
. Для выбора события из журналов Event Viewer мы воспользуемся командлетом Get-WinEvent.
Следующий PowerShell скрипт выведет история входа пользователей на текущий компьютер и представит ее в виде графической таблицы Out-GridView.
$query = @'
<QueryList>
<Query Id='0' Path='Security'>
<Select Path='Security'>
*[System[EventID='4624']
and(
EventData[Data[@Name='VirtualAccount']='%%1843']
and
EventData[Data[@Name='LogonType']='2']
)
]
</Select>
</Query>
</QueryList>
'@
$properties = @(
@{n='User';e={$_.Properties[5].Value}},
@{n='Domain';e={$_.Properties[6].Value}},
@{n='TimeStamp';e={$_.TimeCreated}}
@{n='LogonType';e={$_.Properties[8].Value}}
)
Get-WinEvent -FilterXml $query | Select-Object $properties|Out-GridView
Если нужно выбрать события входа за последние несколько дней, можно добавить pipe с таким условием:
|Where-Object {$_.TimeStamp -gt '5/10/22'}
Командлет Get-WinEvent позволяет получить информацию с удаленных компьютеров. Например, чтобы получить историю входов с двух компьютеров, выполните следующий скрипт:
'msk-comp1', 'msk-comp2' |
ForEach-Object {
Get-WinEvent -ComputerName $_ -FilterXml $query | Select-Object $properties
}
Если протокол RPC закрыт между компьютерами, вы можете получить данные с удаленных компьютеров с помощью PowerShell Remoting командлета Invoke-Command:
Invoke-Command -ComputerName 'msk-comp1', 'msk-comp2' {Get-WinEvent -FilterXml $query | Select-Object $properties}
Event Id 4624 is generated when a user logon successfully to the computer. This event was written on the computer where an account was successfully logged on or a session created.
Event Id 4624 logon type specifies the type of logon session created. The most commonly used logon types for this event are 2 – interactive logon and 3 – network logon.
This event logs on the account logged on, It helps to monitor actions on the computer like anomalies or malicious actions, non-active account login attempts, external accounts and so many others.
In this article, we will discuss Windows event id 4624 logon types, event field information, and security monitoring recommendations.
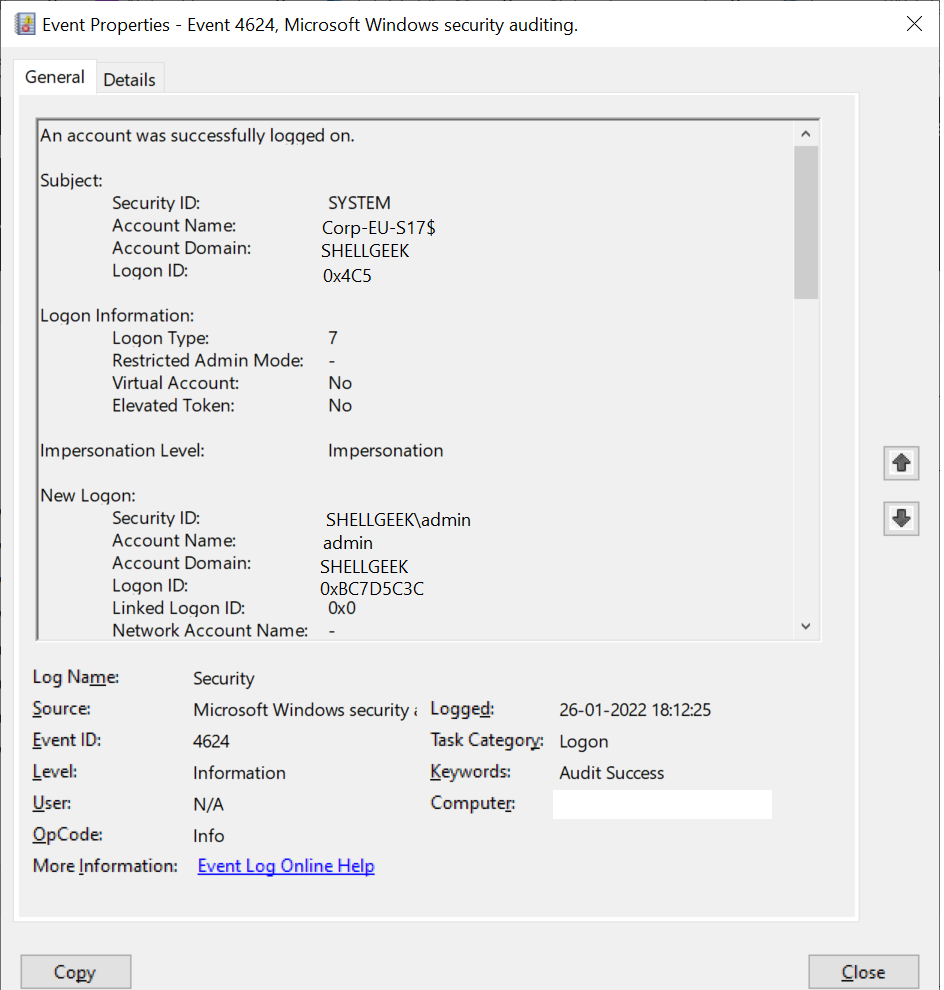
Event Id 4624 – Description
Event code 4624 provides detailed information about an account, logon information, network, and detailed authentication information.
This event is generated on domain controllers (DC), workstations, and systems.
An account was successfully logged on.
Subject:
Security ID: SYSTEM
Account Name: Corp-EU-S17$
Account Domain: SHELLGEEK
Logon ID: 0x4C5
Logon Information:
Logon Type: 7
Restricted Admin Mode: -
Virtual Account: No
Elevated Token: No
Impersonation Level: Impersonation
New Logon:
Security ID: SHELLGEEK\admin
Account Name: admin
Account Domain: SHELLGEEK
Logon ID: 0xBC7D5C3C
Linked Logon ID: 0x0
Network Account Name: -
Network Account Domain: -
Logon GUID: {00000000-0000-0000-0000-000000000000}
Process Information:
Process ID: 0x438
Process Name: C:\Windows\System32\lsass.exe
Network Information:
Workstation Name: Corp-EU-S17
Source Network Address: -
Source Port: -
Detailed Authentication Information:
Logon Process: Negotiate
Authentication Package: Negotiate
Transited Services: -
Package Name (NTLM only):-
Key Length: 0
This event is generated when a logon session is created. It is generated on the computer that was accessed.
The subject fields indicate the account on the local system which requested the logon. This is most commonly a service such as the Server service, or a local process such as Winlogon.exe or Services.exe.
The logon type field indicates the kind of logon that occurred. The most common types are 2 (interactive) and 3 (network).
The New Logon fields indicate the account for whom the new logon was created, i.e. the account that was logged on.
The network fields indicate where a remote logon request originated. Workstation name is not always available and may be left blank in some cases.
The impersonation level field indicates the extent to which a process in the logon session can impersonate.
The authentication information fields provide detailed information about this specific logon request.
- Logon GUID is a unique identifier that can be used to correlate this event with a KDC event.
- Transited services indicate which intermediate services have participated in this logon request.
- Package name indicates which sub-protocol was used among the NTLM protocols.
- Key length indicates the length of the generated session key. This will be 0 if no session key was requested.Fields Description:
Subject:
- Security ID: SID of an account
- Account Name: It specifies the name of the account.
- Account Domain: Computer domain or subject domain name.
- Logon ID: hexadecimal number which helps you to correlate this event ID 4624 with a recent event that might contain the same Logon ID. For ex. Event code 4634: “An account was logged off”
Logon Information
- Logon Type: It provides an integer value that provides information about the type of logon occured on the computer.
- Restricted Admin Mode: It provides value if RemoteInteractive logon type sessions occur. It contains the Yes/No flag value which indicates if the credentials used during the RDP session using Restricted Admin mode. If it is not RemoteInteractive logon, this field will display a “-” string.
- Virtual Account: It provides the Yes or No flag value which indicates if the account is a virtual account.
- Elevated Token: It provides the Yes or No flag value. If it has a Yes value, it means the created logon session is elevated and has administrator privileges.
Impersonation Level
Impersonation level can have one of these value
- SecurityAnonynymous: displayed as an empty string. The server process cannot object identification information about the client and cannot impersonate the client.
- SecurityIdentification: displayed as “Identification”. The server process can obtain information about the client, but it cannot impersonate the client.
- SecurityImpersonation: displayed as “Impersonation“. The server process can impersonate the client’s information. This is the most common type.
- SecurityDelegation: displayed as “Delegation“. The server process can impersonate the client information on a remote system.
New Logon
- Security ID: SID of an account for which logon was occured.
- Account Name: The name of an account for which logon was occured.
- Account Domain: The computer domain name or subject’s domain name.
- Logon ID: Hexadecimal value which helps you to correlate the recent events that might contain the same Logon Id.
- Linked Logon ID: Hexadecimal value of the paired session.
- Network Account Name: It provides a domain for the user and value for NewCredentials logon type. Mostly its value is “-“.
- Logon GUID: It provides a GUID that can help you to correlate this Windows event id 4624 with another event that might contain the same Logon GUID.
Process Information
- Process ID: Process id is the process that attempted logon.
- Process Name: Full path and name of executable for the process.
Network Information
- Workstation Name: computer name from which logon attempt was occurred.
- Source Network Address: IP address of a machine from which logon attempt was performed.
- Source Port: Source port of machine from which logon attempt was occured.
Detailed Authentication Information:
- Logon Process: It specifies the trusted logon process that was used for logon.
- Authentication Package: It specifies the name of authentication package that was used for logon authentication process.
- Transited Services: The list of transmitted services.
- Package Name: The name of the LAN manager sub-package which was used during logon.
- Key Length: The length of the NTLM session security key.
Cool Tip: How to manipulate Active Directory UserAccountControl flags in PowerShell!
Event ID 4624 logon types
The Logon type is of type Int32. It specifies the type of logon which was occurred.
Refer to the list of event code 4624 logon types with a logon title and their description.
| Logon Type | Logon Title | Description |
|---|---|---|
0 |
System |
Used only by the System account, for example at system startup. |
2 |
Interactive |
A user logged on to this computer. |
3 |
Network |
A user or computer logged on to this computer from the network. |
4 |
Batch |
Batch logon type is used by batch servers, where processes may be executing on behalf of a user without their direct intervention. |
5 |
Service |
A service was started by the Service Control Manager. |
7 |
Unlock |
This workstation was unlocked. |
8 |
NetworkCleartext |
A user logged on to this computer from the network. The user’s password was passed to the authentication package in its unhashed form. The built-in authentication packages all hash credentials before sending them across the network. The credentials do not traverse the network in plaintext (also called cleartext). |
9 |
NewCredentials |
A caller cloned its current token and specified new credentials for outbound connections. The new logon session has the same local identity, but uses different credentials for other network connections. |
10 |
RemoteInteractive |
A user logged on to this computer remotely using Terminal Services or Remote Desktop. |
11 |
CachedInteractive |
A user logged on to this computer with network credentials that were stored locally on the computer. The domain controller was not contacted to verify the credentials. |
12 |
CachedRemoteInteractive |
Same as RemoteInteractive. This is used for internal auditing. |
13 |
CachedUnlock |
Workstation logon. |
Get Event log for Event Id 4624 using PowerShell
You can retrieve the event logs for event id 4624 using PowerShell cmdlets like Get-EventLog or Get-WinEvent
Let’s try to get event id 4624 event log using Get-EventLog cmdlet in PowerShell.
$Date = [DateTime]::Now.AddDays(-1)
Get-EventLog -LogName "Security" -After $Date | Where -FilterScript {$_.EventID -eq 4624}
In the above script,
Get-EventLog gets event id 4624 logs for a date using the $Date variable.
It uses the LogName parameter to specify the log name as Security for this event and the Event Id is equal to 4624.
The output of the above Get-EventLog to get this event id log is
Index Time EntryType Source InstanceID Message
----- ---- --------- ------ ---------- -------
20033758 Jan 26 22:04 SuccessA... Microsoft-Windows... 4624 An account was successfully logged on....
20033006 Jan 26 21:49 SuccessA... Microsoft-Windows... 4624 An account was successfully logged on....
20032288 Jan 26 21:34 SuccessA... Microsoft-Windows... 4624 An account was successfully logged on....
20031576 Jan 26 21:19 SuccessA... Microsoft-Windows... 4624 An account was successfully logged on....
20031572 Jan 26 21:19 SuccessA... Microsoft-Windows... 4624 An account was successfully logged on....
20031303 Jan 26 21:14 SuccessA... Microsoft-Windows... 4624 An account was successfully logged on....You can also get event logs for event code 4624 using the Get-WinEvent cmdlet in PowerShell.
Get-WinEvent -FilterHashtable @{LogName = 'Security'; ID = 4624} -MaxEvents 10
In the above PowerShell script,
Get-WinEvent gets event log for event id 4624.
It uses the FilterHashtable parameter and LogName as Security to get these events.
The output of the above command is:
ProviderName: Microsoft-Windows-Security-Auditing
TimeCreated Id LevelDisplayName Message
----------- -- ---------------- -------
26-01-2022 22:04:21 4624 Information An account was successfully logged on....
26-01-2022 21:49:21 4624 Information An account was successfully logged on....
26-01-2022 21:34:21 4624 Information An account was successfully logged on....
26-01-2022 21:19:57 4624 Information An account was successfully logged on....
26-01-2022 21:19:54 4624 Information An account was successfully logged on....
26-01-2022 21:14:27 4624 Information An account was successfully logged on....
26-01-2022 21:07:51 4624 Information An account was successfully logged on....
26-01-2022 20:50:07 4624 Information An account was successfully logged on....
26-01-2022 20:45:50 4624 Information An account was successfully logged on....
26-01-2022 20:36:21 4624 Information An account was successfully logged on....Window Security Event Id 4624 – Examples
Event Code 4624 logon type 5 – Service started by SCM
Event Id 4624 logon type 5 logs message when the service was started by the Service Control Manager (SCM).
An account was successfully logged on.
Subject:
Security ID: SYSTEM
Account Name: Corp-EU-S17$
Account Domain: SHELLGEEK
Logon ID: 0x3E7
Logon Information:
Logon Type: 5
Restricted Admin Mode: -
Virtual Account: No
Elevated Token: Yes
Impersonation Level: Impersonation
New Logon:
Security ID: SYSTEM
Account Name: SYSTEM
Account Domain: NT AUTHORITY
Logon ID: 0x3E7
Linked Logon ID: 0x0
Network Account Name: -
Network Account Domain: -
Logon GUID: {00000000-0000-0000-0000-000000000000}
Process Information:
Process ID: 0x41c
Process Name: C:\Windows\System32\services.exe
Network Information:
Workstation Name: -
Source Network Address: -
Source Port: -
Detailed Authentication Information:
Logon Process: Advapi
Authentication Package: Negotiate
Transited Services: -
Package Name (NTLM only): -
Key Length: 0
This event is generated when a logon session is created. It is generated on the computer that was accessed.
The subject fields indicate the account on the local system which requested the logon. This is most commonly a service such as the Server service, or a local process such as Winlogon.exe or Services.exe.
The logon type field indicates the kind of logon that occurred. The most common types are 2 (interactive) and 3 (network).
The New Logon fields indicate the account for whom the new logon was created, i.e. the account that was logged on.
The network fields indicate where a remote logon request originated. Workstation name is not always available and may be left blank in some cases.
The impersonation level field indicates the extent to which a process in the logon session can impersonate.
The authentication information fields provide detailed information about this specific logon request.
- Logon GUID is a unique identifier that can be used to correlate this event with a KDC event.
- Transited services indicate which intermediate services have participated in this logon request.
- Package name indicates which sub-protocol was used among the NTLM protocols.
- Key length indicates the length of the generated session key. This will be 0 if no session key was requested.Event Id 4624 displays the logon process name as Advapi which was used for logon.
Conclusion
I hope the above article on Event Id 4624 is useful to you.
This event helps you to monitor the type of account logon activity on the computer system.
Using Event Code 4624, you can monitor high-value accounts, anomalies, or malicious actions on the computer using New log on \Security Id to monitor how and when a particular account is being used.
Cool Tip: Event Id 4771 – Kerberos pre-authentication failed!
You can find more topics about PowerShell Active Directory commands and PowerShell basics on the ShellGeek home page.
You can read more on other Windows security and system event logs as given:
- Event Id 4625 0xc000006a – Account Failed to Log on
- Event Id 4634 – An Account was logged off
- Error Code 0xc0000234 – Event Id 4776 – Fix
- Event Id 4670 – System restart or shutdown
| Operating Systems |
Windows 2008 R2 and 7
Windows 2012 R2 and 8.1 Windows 2016 and 10 Windows Server 2019 and 2022 |
|
Category • Subcategory |
Logon/Logoff • Logon |
| Type | Success |
|
Corresponding events in Windows 2003 and before |
528 , 540
|
4624: An account was successfully logged on
On this page
- Description of this event
- Field level details
- Examples
- Discuss this event
- Mini-seminars on this event
This is a highly valuable event since it documents each and every successful attempt to logon to the local computer regardless of logon type, location of the user or type of account. You can tie this event to logoff events 4634 and 4647 using Logon ID.
Win2012 adds the Impersonation Level field as shown in the example.
Win2016/10 add further fields explained below.
Free Security Log Resources by Randy
- Free Security Log Quick Reference Chart
- Windows Event Collection: Supercharger Free Edtion
- Free Active Directory Change Auditing Solution
- Free Course: Security Log Secrets
Description Fields in
4624
Subject:
Identifies the account that requested the logon — NOT the user who just logged on. Subject is usually Null or one of the Service principals and not usually useful information. See New Logon for who just logged on to the sytem.
- Security ID
- Account Name
- Account Domain
- Logon ID
Logon Information:
- Logon Type: See below
Remaining logon information fields are new to Windows 10/2016
- Restricted Admin Mode: Normally «-«.»Yes» for incoming Remote Desktop Connections where the client specified /restrictedAdmin on the command line. Restricted admin mode is an important way to limit the spread of admin credentials in ways they can be harvested by malware using pass-the-hash and related techniques. You should only see with for logon type 10. When you remote desktop into a server with /restrictedAdmin you get full authority on that server but it doesn’t carry with you if you access other systems from within that RDP session. This field allows you to detect RDP sessions that fail to use restricted admin mode.
- Virtual Account: Normally «No». This will be Yes in the case of services configured to logon with a «Virtual Account». Virtual Accounts only come up in Service logon types (type 5), when Windows starts a logon session in connection with a service starting up. You can configure services to run as a virtual account which is what Microsoft calls a «managed local account». They’re «domain» is «NT Service» as in an instance of MS SQL Server named Supercharger running as NT SERVICE\MSSQL$SUPERCHARGER.
- Elevated Token: Yes or No. It will be Yes if the user is a member of Administrators — kind of… The «kind of» applies to interactive logons, when you are an admin and you have User Account Control (UAC) enabled. Then when you logon you actually get 2 logon sessions. One without the Administrators SID and related privileges in your security token and another session with all that authority. Everything you do happens under the unprivileged logon session until you attempt to run something requiring admin authority. After you approve the UAC dialog box, Windows runs that one operation under the other logon sesson. So in the log you will see 2 of these events, one where this field is Yes and other No. The 2 logon sessions are connected by the Linked Logon ID described below.
Logon Type:
This is a valuable piece of information as it tells you HOW the user just logged on:
|
Logon Type
|
Description
|
| 2 | Interactive (logon at keyboard and screen of system) |
| 3 | Network (i.e. connection to shared folder on this computer from elsewhere on network) |
| 4 | Batch (i.e. scheduled task) |
| 5 | Service (Service startup) |
| 7 | Unlock (i.e. unnattended workstation with password protected screen saver) |
| 8 | NetworkCleartext (Logon with credentials sent in the clear text. Most often indicates a logon to IIS with «basic authentication») See this article for more information. |
| 9 | NewCredentials such as with RunAs or mapping a network drive with alternate credentials. This logon type does not seem to show up in any events. If you want to track users attempting to logon with alternate credentials see 4648. MS says «A caller cloned its current token and specified new credentials for outbound connections. The new logon session has the same local identity, but uses different credentials for other network connections.» |
| 10 | RemoteInteractive (Terminal Services, Remote Desktop or Remote Assistance) |
| 11 | CachedInteractive (logon with cached domain credentials such as when logging on to a laptop when away from the network) |
Impersonation Level: (Win2012 and later)
From MSDN
| Anonymous | Anonymous COM impersonation level that hides the identity of the caller. Calls to WMI may fail with this impersonation level. |
| Default | Default impersonation. |
| Delegate | Delegate-level COM impersonation level that allows objects to permit other objects to use the credentials of the caller. This level, which will work with WMI calls but may constitute an unnecessary security risk, is supported only under Windows 2000. |
| Identify | Identify-level COM impersonation level that allows objects to query the credentials of the caller. Calls to WMI may fail with this impersonation level. |
| Impersonate | Impersonate-level COM impersonation level that allows objects to use the credentials of the caller. This is the recommended impersonation level for WMI calls. |
New Logon:
The user who just logged on is identified by the Account Name and Account Domain. You can determine whether the account is local or domain by comparing the Account Domain to the computer name. If they match, the account is a local account on that system, otherwise a domain account.
- Security ID: the SID of the account
- Account Name: Logon name of the account
- Account Domain: Domain name of the account in either the DNS name (can be upper or lowercase) or pre-Win2k NETBIOS domain name. In the case of special subjects (well known security principals) like SYSTEM, LOCAL SERVICE, NETWORK SERVICE, ANONYMOUS LOGON this field will be «NT AUTHORITY». It can also be «NT Service» as in the case of virtual accounts for services. See above. Finally, if the account is a local account, this field will be the name of the computer.
- Logon ID: a semi-unique (unique between reboots) number that identifies the logon session just initiated. Any events logged subsequently during this logon session will report the same Logon ID through to the logoff event 4647 or 4634.
- Linked Login ID: (Win2016/10) This is relevant to User Account Control and interactive logons. When an admin logs on interactively to a system with UAC enabled, Windows actually creates 2 logon sessions — one with and one without privilege. This is called a split token and this fields links the 2 sessions to each other. See Elevated Token above.
- Network Account Name: (Win2016/10) This appears to always be «-«. It seems connected to LogonUser() with LOGON32_LOGON_NEW_CREDENTIALS but I’ve not been able to produce an example. If you have an event with this field filled in please open a forum posting on this page and let us see it.
- Network Account Domain: (Win2016/10) see above
- Logon GUID: Supposedly you should be able to correlate logon events on this computer with corresonding authentication events on the domain controller using this GUID. Such as linking 4624 on the member computer to 4769 on the DC. But the GUIDs do not match between logon events on member computers and the authentication events on the domain controller.
Process Information:
- Process ID is the process ID specified when the executable started as logged in 4688.
- Process Name: identifies the program executable that processed the logon. This is one of the trusted logon processes identified by 4611.
Network Information:
This section identifies WHERE the user was when he logged on. Of course if logon is initiated from the same computer this information will either be blank or reflect the same local computers.
- Workstation Name: the computer name of the computer where the user is physically present in most cases unless this logon was intitiated by a server application acting on behalf of the user. Workstation may also not be filled in for some Kerberos logons since the Kerberos protocol doesn’t really care about the computer account in the case of user logons and therefore lacks any field for carrying workstation name in the ticket request message.
- Source Network Address: the IP address of the computer where the user is physically present in most cases unless this logon was intitiated by a server application acting on behalf of the user. If this logon is initiated locally the IP address will sometimes be 127.0.0.1 instead of the local computer’s actual IP address. This field is also blank sometimes because Microsoft says «Not every code path in Windows Server 2003 is instrumented for IP address, so it’s not always filled out.»
- Source Port: identifies the source TCP port of the logon request which seems useless since with most protocols source ports are random.
Detailed Authentication Information:
- Logon Process: (see 4611) CredPro indicates a logon initiated by User Account Control
- Authentication Package: (see 4610 or 4622)
- Transited Services: This has to do with server applications that need to accept some other type of authentication from the client and then transition to Kerberos for accessing other resources on behalf of the client. See http://msdn.microsoft.com/msdnmag/issues/03/04/SecurityBriefs/. MS says: Transmitted services are populated if the logon was a result of a S4U (Service For User) logon process. S4U is a Microsoft extension to the Kerberos Protocol to allow an application service to obtain a Kerberos service ticket on behalf of a user – most commonly done by a front-end website to access an internal resource on behalf of a user. For more information about S4U, see https://msdn.microsoft.com/en-us/library/cc246072.aspx
- Package name: If this logon was authenticated via the NTLM protocol (instead of Kerberos for instance) this field tells you which version of NTLM was used. See security option «Network security: LAN Manager authentication level». This field only populated if Authentication Package = NTLM. Possible values: “NTLM V1”, “NTLM V2”, “LM”
- Key Length: Length of key protecting the «secure channel». See security option «Domain Member: Require strong (Windows 2000 or later) session key». If value is 0 this would indicate security option «Domain Member: Digitally encrypt secure channel data (when possible)» failed. MS says the length of NTLM Session Security key. Typically it has 128 bit or 56 bit length. This parameter is always 0 if “Authentication Package” = “Kerberos”, because it is not applicable for Kerberos protocol. This field will also have “0” value if Kerberos was negotiated using Negotiate authentication package.
Supercharger Free Edition
Centrally manage WEC subscriptions.
Free.
Examples of 4624
Windows 10 and 2016
An account was successfully logged on.
Subject:
Security ID: SYSTEM
Account Name: DESKTOP-LLHJ389$
Account Domain: WORKGROUP
Logon ID: 0x3E7
Logon Information:
Logon Type: 7
Restricted Admin Mode: —
Virtual Account: No
Elevated Token: No
Impersonation Level: Impersonation
New Logon:
Security ID: AzureAD\RandyFranklinSmith
Account Name: rsmith@montereytechgroup.com
Account Domain: AzureAD
Logon ID: 0xFD5113F
Linked Logon ID: 0xFD5112A
Network Account Name: —
Network Account Domain: —
Logon GUID: {00000000-0000-0000-0000-000000000000}
Process Information:
Process ID: 0x30c
Process Name: C:\Windows\System32\lsass.exe
Network Information:
Workstation Name: DESKTOP-LLHJ389
Source Network Address: —
Source Port: —
Detailed Authentication Information:
Logon Process: Negotiat
Authentication Package: Negotiate
Transited Services: —
Package Name (NTLM only): —
Key Length: 0
Win2008
An account was successfully logged on.
Subject:
Security ID: SYSTEM
Account Name: WIN-R9H529RIO4Y$
Account Domain: WORKGROUP
Logon ID: 0x3e7
Logon Type:10
New Logon:
Security ID: WIN-R9H529RIO4Y\Administrator
Account Name: Administrator
Account Domain: WIN-R9H529RIO4Y
Logon ID: 0x19f4c
Logon GUID: {00000000-0000-0000-0000-000000000000}
Process Information:
Process ID: 0x4c0
Process Name: C:\Windows\System32\winlogon.exe
Network Information:
Workstation Name: WIN-R9H529RIO4Y
Source Network Address: 10.42.42.211
Source Port: 1181
Detailed Authentication Information:
Logon Process: User32
Authentication Package: Negotiate
Transited Services: —
Package Name (NTLM only): —
Key Length: 0
This event is generated when a logon session is created. It is generated on the computer that was accessed.
The subject fields indicate the account on the local system which requested the logon. This is most commonly a service such as the Server service, or a local process such as Winlogon.exe or Services.exe.
The logon type field indicates the kind of logon that occurred. The most common types are 2 (interactive) and 3 (network).
The New Logon fields indicate the account for whom the new logon was created, i.e. the account that was logged on.
The network fields indicate where a remote logon request originated. Workstation name is not always available and may be left blank in some cases.
The authentication information fields provide detailed information about this specific logon request.
The authentication information fields provide detailed information about this specific logon request.
- Logon GUID is a unique identifier that can be used to correlate this event with a KDC event.
- Transited services indicate which intermediate services have participated in this logon request.
- Package name indicates which sub-protocol was used among the NTLM protocols.
- Key length indicates the length of the generated session key. This will be 0 if no session key was requested.
Win2012
An account was successfully logged on.
Subject:
Security ID: NULL SID
Account Name: —
Account Domain: —
Logon ID: 0x0
Logon Type: 3
Impersonation Level: Impersonation
New Logon:
Security ID: LB\DEV1$
Account Name: DEV1$
Account Domain: LB
Logon ID: 0x894B5E95
Logon GUID: {f09e5f81-9f19-5f11-29b8-8750c7c02be3}
Process Information:
Process ID: 0x0
Process Name: —
Network Information:
Workstation Name:
Source Network Address: 10.42.1.161
Source Port: 59752
Detailed Authentication Information:
Logon Process: Kerberos
Authentication Package: Kerberos
Transited Services: —
Package Name (NTLM only): —
Key Length: 0
Top 10 Windows Security Events to Monitor
Free Tool for Windows Event Collection
- Understanding Logon Events in the Windows Server 2022 Security Log
- Top 6 Security Events You Only Detect by Monitoring Workstation Security Logs
|