Microsoft Teams is indispensable in our work life these days. Nothing is more annoying than an error message like ‘aadsts50020’, when you need Microsoft Teams the most.
Tech Support 24/7
Ask a Tech Specialist Online
Connect with the Expert via email, text or phone. Include photos, documents, and more. Get step-by-step instructions from verified Tech Support Specialists.
On this page, you will find more information about the most common causes and most relevant solutions for the Microsoft Teams error ‘aadsts50020’. Do you need help straight away? Visit our support page.
Error information
How to solve Microsoft Teams error aadsts50020
We’ve created a list of solutions which you can follow if you want to solve this Microsoft Teams problem yourself. Do you need more help? Visit our support page if you need professional support with Microsoft Teams right away.
Tech Support 24/7
Ask a Tech Specialist Online
Connect with the Expert via email, text or phone. Include photos, documents, and more. Get step-by-step instructions from verified Tech Support Specialists.
Have you found a solution yourself, but it is not in the list? Share your solution in the comments below.
Need more help?
Do you need more help?
Tech experts are ready to answer your questions.
Ask a question
Search code, repositories, users, issues, pull requests…
Provide feedback
Saved searches
Use saved searches to filter your results more quickly
Sign up
| title | description | ms.date | author | ms.author | ms.editor | ms.reviewer | ms.service | ms.subservice | keywords |
|---|---|---|---|---|---|---|---|---|---|
|
Error AADSTS50020 — User account from identity provider does not exist in tenant |
Troubleshoot scenarios in which a guest user unsuccessfully tries to sign in to the resource tenant and error code AADSTS50020 is returned. |
03/28/2023 |
DennisLee-DennisLee |
v-dele |
v-jsitser |
rrajan,haelshab,sungow |
active-directory |
app-mgmt |
Error AADSTS50020 — User account from identity provider does not exist in tenant
This article helps you troubleshoot error code AADSTS50020 that’s returned if a guest user from an identity provider (IdP) can’t sign in to a resource tenant in Azure Active Directory (Azure AD).
Symptoms
When a guest user tries to access an application or resource in the resource tenant, the sign-in fails, and the following error message is displayed:
AADSTS50020: User account ‘user@domain.com’ from identity provider {IdentityProviderURL} does not exist in tenant {ResourceTenantName}.
When an administrator reviews the sign-in logs on the home tenant, a «90072» error code entry indicates a sign-in failure. The error message states:
User account {email} from identity provider {idp} does not exist in tenant {tenant} and cannot access the application {appId}({appName}) in that tenant. The account needs to be added as an external user in the tenant first. Sign out and sign in again with a different Azure Active Directory user account.
Cause 1: Used unsupported account type (multitenant and personal accounts)
If your app registration is set to a single-tenant account type, users from other directories or identity providers can’t sign in to that application.
Solution: Change the sign-in audience setting in the app registration manifest
To make sure that your app registration isn’t a single-tenant account type, perform the following steps:
-
In the Azure portal, search for and select App registrations.
-
Select the name of your app registration.
-
In the sidebar, select Manifest.
-
In the JSON code, find the signInAudience setting.
-
Check whether the setting contains one of the following values:
- AzureADandPersonalMicrosoftAccount
- AzureADMultipleOrgs
- PersonalMicrosoftAccount
If the signInAudience setting doesn’t contain one of these values, re-create the app registration by having the correct account type selected. You currently can’t change signInAudience in the manifest.
For more information about how to register applications, see Quickstart: Register an application with the Microsoft identity platform.
Cause 2: Used the wrong endpoint (personal and organization accounts)
Your authentication call must target a URL that matches your selection if your app registration’s supported account type was set to one of the following values:
-
Accounts in any organizational directory (Any Azure AD directory — Multitenant)
-
Accounts in any organizational directory (Any Azure AD directory — Multitenant) and personal Microsoft accounts (e.g. Skype, Xbox)
-
Personal Microsoft accounts only
If you use https://login.microsoftonline.com/<YourTenantNameOrID>, users from other organizations can’t access the application. You have to add these users as guests in the tenant that’s specified in the request. In that case, the authentication is expected to be run on your tenant only. This scenario causes the sign-in error if you expect users to sign in by using federation with another tenant or identity provider.
Solution: Use the correct sign-in URL
Use the corresponding sign-in URL for the specific application type, as listed in the following table:
| Application type | Sign-in URL |
|---|---|
| Multitenant applications | https://login.microsoftonline.com/organizations |
| Multitenant and personal accounts | https://login.microsoftonline.com/common |
| Personal accounts only | https://login.microsoftonline.com/consumers |
In your application code, apply this URL value in the Authority setting. For more information about Authority, see Microsoft identity platform application configuration options.
Cause 3: Signed in to the wrong tenant
When users try to access your application, either they’re sent a direct link to the application, or they try to gain access through https://myapps.microsoft.com. In either situation, users are redirected to sign in to the application. In some cases, the user might already have an active session that uses a different personal account than the one that’s intended to be used. Or they have a session that uses their organization account although they intended to use a personal guest account (or vice versa).
To make sure that this scenario is the issue, look for the User account and Identity provider values in the error message. Do those values match the expected combination or not? For example, did a user sign in by using their organization account to your tenant instead of their home tenant? Or did a user sign in to the live.com identity provider by using a different personal account than the one that was already invited?
Solution: Sign out, then sign in again from a different browser or a private browser session
Instruct the user to open a new in-private browser session or have the user try to access from a different browser. In this case, users must sign out from their active session, and then try to sign in again.
Cause 4: Guest user wasn’t invited
The guest user who tried to sign in was not invited to the tenant.
Solution: Invite the guest user
Make sure that you follow the steps in Quickstart: Add guest users to your directory in the Azure portal to invite the guest user.
Cause 5: App requires user assignment
If your application is an enterprise application that requires user assignment, error AADSTS50020 occurs if the user isn’t on the list of allowed users who are assigned access to the application. To check whether your enterprise application requires user assignment:
-
In the Azure portal, search for and select Enterprise applications.
-
Select your enterprise application.
-
In the sidebar, select Properties.
-
Check whether the Assignment required option is set to Yes.
Solution: Assign access to users individually or as part of a group
Use one of the following options to assign access to users:
-
To individually assign the user access to the application, see Assign a user account to an enterprise application.
-
To assign users if they’re a member of an assigned group or a dynamic group, see Manage access to an application.
Cause 6: Tried to use a resource owner password credentials flow for personal accounts
If a user tries to use the resource owner password credentials (ROPC) flow for personal accounts, error AADSTS50020 occurs. The Microsoft identity platform supports ROPC only within Azure AD tenants, not personal accounts.
Solution: Use an endpoint that’s specific to the tenant or organization
Use a tenant-specific endpoint (https://login.microsoftonline.com/<TenantIDOrName>) or the organization’s endpoint. Personal accounts that are invited to an Azure AD tenant can’t use ROPC. For more information, see Microsoft identity platform and OAuth 2.0 Resource Owner Password Credentials.
Cause 7: A previously deleted user name was re-created by the home tenant administrator
Error AADSTS50020 might occur if the name of a guest user who was deleted in a resource tenant is re-created by the administrator of the home tenant. To verify that the guest user account in the resource tenant isn’t associated with a user account in the home tenant, use one of the following options:
Verification option 1: Check whether the resource tenant’s guest user is older than the home tenant’s user account
The first verification option involves comparing the age of the resource tenant’s guest user against the home tenant’s user account. You can make this verification by using Microsoft Graph or MSOnline PowerShell.
Microsoft Graph
Issue a request to the MS Graph API to review the user creation date, as follows:
GET https://graph.microsoft.com/v1.0/users/{id | userPrincipalName}/createdDateTime
Then, check the creation date of the guest user in the resource tenant against the creation date of the user account in the home tenant. The scenario is confirmed if the guest user was created before the home tenant’s user account was created.
MSOnline PowerShell
[!NOTE]
The MSOnline PowerShell module is set to be deprecated.
Because it’s also incompatible with PowerShell Core, make sure that you’re using a compatible PowerShell version so that you can run the following commands.
Run the Get-MsolUser PowerShell cmdlet to review the user creation date, as follows:
Get-MsolUser -SearchString user@contoso.com | Format-List whenCreated
Then, check the creation date of the guest user in the resource tenant against the creation date of the user account in the home tenant. The scenario is confirmed if the guest user was created before the home tenant’s user account was created.
Verification option 2: Check whether the resource tenant’s guest alternative security ID differs from the home tenant’s user net ID
[!NOTE]
The MSOnline PowerShell module is set to be deprecated.
Because it’s also incompatible with PowerShell Core, make sure that you’re using a compatible PowerShell version so that you can run the following commands.
When a guest user accepts an invitation, the user’s LiveID attribute (the unique sign-in ID of the user) is stored within AlternativeSecurityIds in the key attribute. Because the user account was deleted and created in the home tenant, the NetID value for the account will have changed for the user in the home tenant. Compare the NetID value of the user account in the home tenant against the key value that’s stored within AlternativeSecurityIds of the guest account in the resource tenant, as follows:
-
In the home tenant, retrieve the value of the
LiveIDattribute using theGet-MsolUserPowerShell cmdlet:Get-MsolUser -SearchString tuser1 | Select-Object -ExpandProperty LiveID -
In the resource tenant, convert the value of the
keyattribute withinAlternativeSecurityIdsto a base64-encoded string:[convert]::ToBase64String((Get-MsolUser -ObjectId 01234567-89ab-cdef-0123-456789abcdef ).AlternativeSecurityIds.key) -
Convert the base64-encoded string to a hexadecimal value by using an online converter (such as base64.guru).
-
Compare the values from step 1 and step 3 to verify that they’re different. The
NetIDof the user account in the home tenant changed when the account was deleted and re-created.
Solution: Reset the redemption status of the guest user account
Reset the redemption status of the guest user account in the resource tenant. Then, you can keep the guest user object without having to delete and then re-create the guest account. You can reset the redemption status by using the Azure portal, Azure PowerShell, or the Microsoft Graph API. For instructions, see Reset redemption status for a guest user.
[!INCLUDE Azure Help Support]
I am developing a desktop app with Java for a uni project and I have used Azure Active Directory to register the app. I am very new with all of this so please forgive me if I have misunderstood something. I had no problems with Azure AD until this week. When logging into the portal I am receiving the following error message:
The portal is having issues getting an authentication token. The experience rendered may be degraded.
Additional information from the call to get a token:
Extension: Microsoft_AAD_IAM
Resource: microsoft.graph
Details: The logged in user is not authorized to fetch tokens for extension ‘Microsoft_AAD_IAM’ because the user account is not a member of tenant ‘f8cdef31-a31e-4b4a-93e4-5f571e91255a’.
Error details: AADSTS50020: User account ‘{EmailHidden}’ from identity provider ‘live.com’ does not exist in tenant ‘Microsoft Services’ and cannot access the application ‘c44b4083-3bb0-49c1-b47d-974e53cbdf3c'(Azure Portal) in that tenant. The account needs to be added as an external user in the tenant first.
Sign out and sign in again with a different Azure Active Directory user account.
Trace ID: 4b11e8b6-8400-4a15-8553-270679f41300
Correlation ID: f0f3259b-9c04-4299-82c3-9d88a994c91c
Timestamp: 2022-04-03 15:02:23Z
This happens every time I try to access ANYTHING on the Azure dashboard. I have tried clearing my browser’s history and cookies, using a private browser, using a different browser, using a different device, using a different network and nothing has worked.
I really don’t know what caused this since I am fairly convinced I didn’t change anything, so I don’t know why the (personal) account I have been using the whole time would now not be a part of the tenant. But since (I think) I am the admin, I have no way of accessing the ‘Users’ page of Azure AD and adding me back to the tenant as a user. I can’t even create a new support request the Help + Support page as it just hangs — probably due to this authentication error.
Any guidance or help would be very much appreciated, thank you.

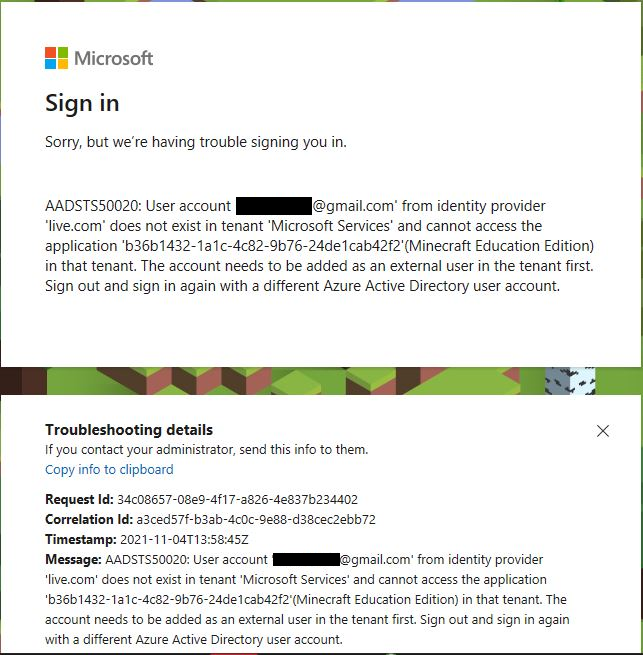
Do you see this error when you or a user in your organization tries to login? «AADSTS50020: User account ‘[email address]‘ from identity provider ‘[identity provider]’ does not exist in tenant ‘Microsoft Services’ and cannot access the application ‘b36b1432-1a1c-4c82-9b76-24de1cab42f2′(Minecraft Education) in that tenant. The account needs to be added as an external user in the tenant first. Sign out and sign in again with a different Azure Active Directory user account.
This error can happen for a few different reasons. Check out the table below for more information.
|
Cause |
Solution |
|
You are logging in with a personal Microsoft account |
|
|
The user account is not an AAD account |
|
|
Camps and Clubs (commercial) account not correctly configured |
|
I am working on an app that manages azure resources for customers (provision VMs, create VNets).
We have created a multi-tenant application in the azure portal that is configured for Delegated permissions of Windows Azure Service Management API and Windows Azure Active Directory.
We are able to login AAD based account without a problem. But when a live.com based account logs in, the user gets a AADSTS50020 error.
We for the login, we are navigating to https://login.microsoftonline.com/common/OAuth2/Authorize
with the following parameters:
client_id=XXX&response_mode=query&response_type=code&redirect_uri=XXX&prompt=consent
Here is the full error message:
AADSTS50020: User account ‘xxx@hotmail.com’ from identity provider
‘live.com’ does not exist in tenant ‘XXX’ and cannot access the
application ‘xxx’ in that tenant. The account needs to be added as an
external user in the tenant first. Sign out and sign in again with a
different Azure Active Directory user account.